Protect Your Business by Protecting Your Browser
Small and medium-sized businesses can make themselves more secure from cyber attacks by understanding entry points, knowing what vulnerabilities exist, and learning how to create a safe browsing experience.
Why Should Small and Medium-Sized Businesses Virtualize in 2022?
When it comes to developing strategies for your business growth and success, it's essential to consider the structure of your network so it's scalable and secure. Moving to a virtualized environment provides small- and medium-sized businesses multiple advantages.
Why Do Hospitals Need Managed IT Services
A managed services provider can keep hospital and healthcare organizations’ IT systems fast, scalable, reliable, and secure while also overseeing and monitoring systems to ensure there are no interruptions, integrate cloud-based technologies, validate information is secure, establish HIPAA compliance, as well as facilitate data backups and recovery initiatives.
Outsourcing Backups to Prevent Data Loss
For small- and mid-size businesses, outsourcing backup and security may be more beneficial than in-house management when it comes to scalability, business continuity and efficiency.
Is it Time—Time to Replace a Server?
Evaluating your server on its performance, cost, warranty coverage, and maintenance will help identify if it’s time to make a change to a more efficient and secure server.
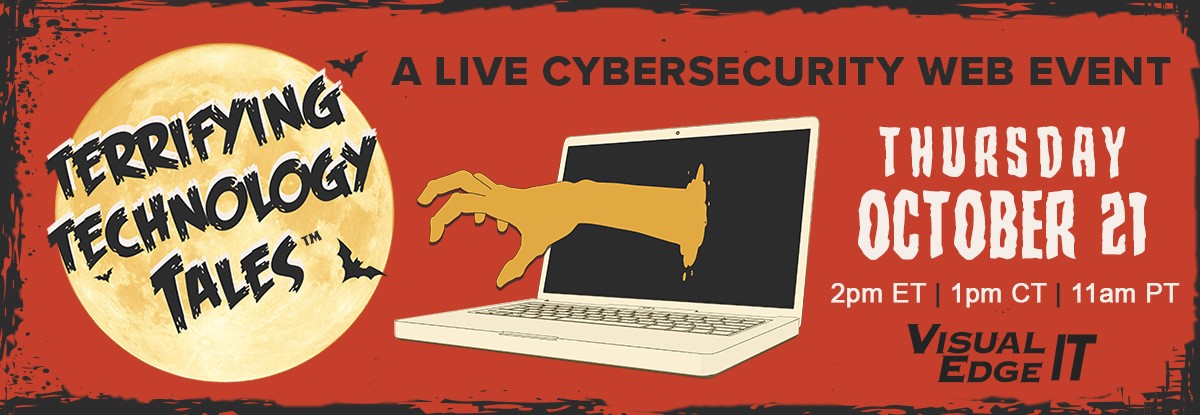
Terrifying Technology Tales Webinar – October 2021
Last month was cybersecurity awareness month. At Visual Edge IT, we are dedicated to keeping your critical infrastructure secure all year long.
Compete For Your Customers… or Someone Else Will!
A business review engages the customer and enables a strategic discussion regarding their business and how technology can be a competitive advantage for them.
Virtualization: Common Challenges and Solutions
Virtualizing a network has its benefits, but it’s important to understand common challenges and solutions around VM sprawl, application performance bottlenecks, and licensing compliance that are common when migrating a system.
Categories
- Alerts (1)
- blog (75)
- Cloud (26)
- Cybersecurity (49)
- Data Backups (16)
- Disaster Recovery (16)
- eGuides (2)
- General Technology Tips (8)
- Inside Wire (2)
- Main Pages (8)
- Managed IT Services (31)
- Managed Security Services (12)
- Office 365 Migration (6)
- PR (1)
- Press Releases (46)
- Print (26)
- Print / Workflow (8)
- Printing Solutions (5)
- Remote Access / Home Office (6)
- Security Tips (38)
- Technology Solutions (25)
- Turnkey IT Services (2)
- VoIP Services (8)
- Webinar (5)
Recent Posts
- Embrace AI for a Competitive Business Advantage
- 3 Steps to Integrate Cyber Insurance into Your Security Framework
- How to Structure IT for Growth: Cultivating a Digital-first Business
- 5 Tips for Building a Resilient Workforce to Counteract Phishing Schemes
- 5 Steps to Reinvent Your Security Posture with Insight from a Virtual CISO